Amazon Web Services (AWS) provides has a number of established security programs and provides compliance certifications for standards including ISO, PCI, and SOC 2. However, it is up to cloud customers to ensure they are compliant in AWS.
Data security and regulatory compliance are essential for organizations and regulated industries moving into the public cloud. For companies utilizing a cloud service provider such as Amazon Web Services (AWS) there are specific requirements for maintain AWS compliance. While AWS provides security programs and certifications, data that is stored in AWS is not automatically compliant.
Most public cloud providers including AWS operation on a Shared Responsibility Model. This means that while AWS is responsible for many physical securities, cloud customers are must handle all administrative and technical securities and safeguards for compliance.
While AWS provides security teams with compliance programs to jumpstart their compliance efforts, organizations must ensure that cloud services are configured in a secure and compliant manner in order to maintain AWS compliance. AWS infrastructure and cloud services can be provisioned and utilized in many ways. Organizations are reasonable for the security configuration of these services.
DevOps teams, responsible for continuous delivery and continuous integration are now responsible for security configuration with AWS cloud services and now have the task of addressing compliance issues and implementing continuous compliance.
Setting Cloud Security Controls
Cloud customers are responsible for ensuring that AWS cloud services have security settings and configuration to address security and compliance controls including: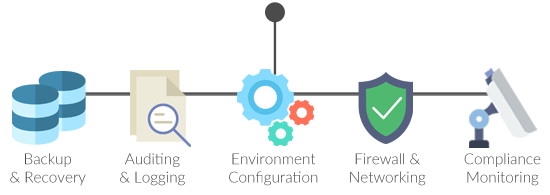
- Backup and Disaster Recovery (DR)
- Audit Logging
- Access Control
- Network and Firewall Settings
- Encryption (in-transit and at-rest)
These security standards may be configured within each individual AWS cloud service. Services such as Amazon S3, Amazon EC2, and Amazon RDS each have different associated resources and security settings. Consider the following security settings for a service such as Amazon S3:
Amazon S3 Security Configuration:
- Ensure S3 bucket is encrypted with server-side encryption
- Ensure S3 bucket enforces encryption in transit
- Ensure S3 bucket have versioning enabled
- Ensure S3 bucket cross-region replication is enabled
- Ensure S3 bucket has object lock enabled (where applicable)
- Ensure S3 Bucket access logging is enabled
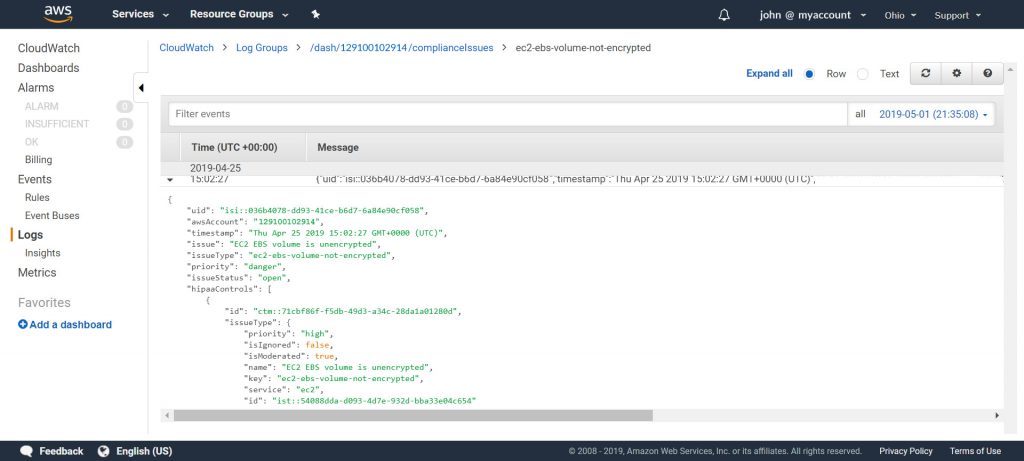
In order to ensure that configuration settings like this are enabled and meet regulatory compliance requirements such as HIPAA, SOC 2, NIST, DevOps teams must analyze the cloud environment using a tool such as AWS Config. When configuration issues are detected for cloud services, these issues may be sent to the DevOps team though Lambda or SNS and may be resolved by triggering specific Lambda functions. Dash ComplyOps can help teams to automate security and compliance controls across cloud services in Amazon Web Services (AWS).
Organizations may monitor security configuration across AWS services, but should map these security controls back to the applicable regulatory requirements in their security program.
AWS Services to Meet Regulatory Compliance
While individual AWS services may have specific security configuration, AWS provides specific services that can be utilized to meet broad security needs around Access Control and Audit Logging. Organizations may consider the following cloud services to address other essential AWS compliance requirements:
AWS Identity Access Management (IAM) can be used to manage identification and user access to sensitive data. Organizations should limit access to AWS services to least necessary users.
Amazon CloudWatch and CloudTrail may be used in order to monitor and collect audit logs for activity across AWS cloud environments.
- CloudWatch allows organizations to collect and aggregate security events and logs. Logs can be used to trigger other security alerts and Lambda functions in AWS.
- CloudTrail can be enabled for AWS accounts and regions in order to track AWS API calls and analyze overall account activity.
Continuous Compliance Monitoring
As organization cloud environments continue to grow, new AWS services may be added. It is important that teams continue to maintain the same security and regulatory compliance standards for new infrastructure that is created within AWS accounts. Continuous compliance monitoring helps ensure that organizations maintain compliance standards across cloud infrastructure.
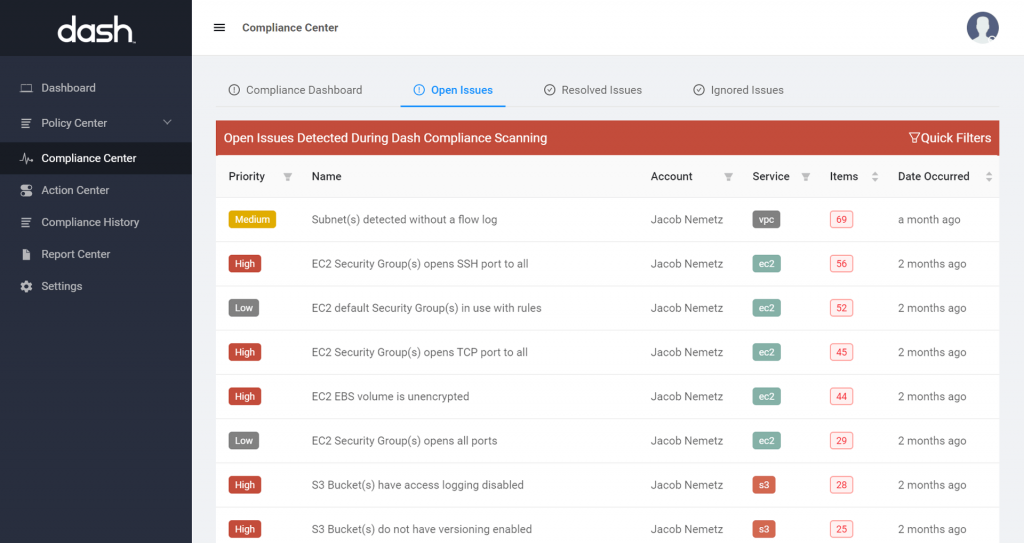
Continuous compliance monitoring tools such as Dash ComplyOps make it easy for teams to build custom security policies and automatically detect and remediate security issues related regulations such as SOC 2, HIPAA, ISO, and NIST. Teams can set regulatory compliance standards, enforce controls, and build compliance reports to demonstrate their security posture. Tools such as ComplyOps streamline AWS compliance process.
Learn more in our Guide to Continuous Compliance Monitoring in the Cloud.